Your company trained all its employees on security awareness training and has or uses a dedicated security team, but will that really protect all access to sensitive data?
The cyber-enabled population can alleviate the pressure of hiring cybersecurity talent by providing organizations with a pipeline of personnel with baseline cybersecurity skills or aptitude. In upskilling or cross-skilling individuals within cyber-enabled roles, organizations can take charge creating their own talent pipeline, rather than waiting for universities or government to impact it in the short-term.
The cybersecurity industry has exploded over the last decade. Overall spending across public and private sectors in the U.S. is estimated at over $44 billion for specific cyber defense people, processes, and technologies. The majority of these funds have traditionally been allocated for cybersecurity technology products and services; however, there is an increasingly concerted effort to address the workforce issue—the yawning cybersecurity skills gap.
Organizations purchase cybersecurity awareness solutions like KnowBe4, Proofpoint, Cofense, and dozens of others. These products and services are designed for the general workforce to increase awareness of common threats like phishing or social engineering. Some estimates suggest this industry will continue to grow at a significant clip to billions of dollars within this decade.
A number of solutions and providers are focused on either cybersecurity awareness or technical cyber training, but the reality is that there is a dire need in the middle—over-served by cybersecurity bootcamps and underserved by awareness training.
What is the cyber-enabled workforce?
The cyber-enabled workforce is a subset of the general working population that, through the role, responsibility, and access, can impact cybersecurity risk or opportunity within an organization.
Leaders of organizations that identify, support, and develop this population are more likely to improve risk management and lower cyber risk. Perhaps more importantly, developing the cyber-enabled population promotes a positive cybersecurity culture while also creating internal candidates for more technical cybersecurity roles.
What is the difference between a cybersecurity and a cyber-enabled role?
In short, cybersecurity roles focus on information security For example, a SOC Analyst is a cybersecurity employee with the majority of his or her work responsibilities directly tied to cybersecurity.
Conversely, cyber-enabled personnel are not primarily responsible for information security, but rather work within IT networks as part of their roles of various departments and experience levels. To illustrate, an accountant within a firm may work with computer systems and have access to sensitive financial data; he or she works within a cyber-enabled role but clearly does not work within a dedicated cybersecurity position.
What level of cybersecurity knowledge and skills does the cyber-enabled workforce need to possess?
The simple answer: a cyber-enabled employee should have an above-average understanding of cybersecurity, but not to the breadth and depth of knowledge of a dedicated cybersecurity practitioner (that comes later). Cyber-enabled employees may work in areas like traditional IT, data security, risk management, and compliance, or threat detection and remediation. Security is a critical aspect of their roles, but they are not specifically related to cybersecurity functions. For the vast majority of cyber-enabled employees, general cybersecurity awareness knowledge (anti-phishing, etc.) is currently offered but is woefully insufficient. To the other extreme, credential-specific training that results in a certification such as CISSP or CEH is expensive and mostly irrelevant to cyber-enabled roles.
How can the cyber-enabled workforce create talent pipeline?
According to the Bureau of Labor Statistics, there are approximately 129 million people employed in full-time positions in the United States. Of those, about 40% work at large or very large companies (52 million people) and another 26% work at medium-sized companies (34 million). While there are certainly cybersecurity and cyber-enabled roles within small businesses, we will focus on medium to large businesses for the sake of simplification and illustration.
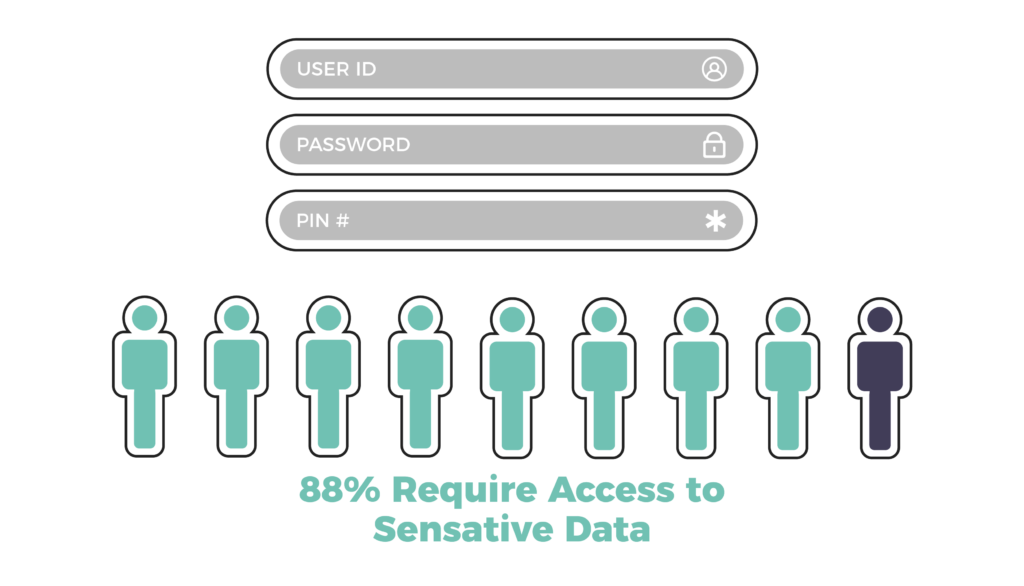
Not all of those 86 million employees employed at medium to large businesses are cyber-enabled, but many of them are. According to a Ponemon study, nearly nine in ten (88%) employees said their jobs require them to access and use proprietary information such as customer data, contact lists, employee records, confidential business documents, or other sensitive data. Based on this projection, the cyber-enabled workforce within the United States exceeds 75 million personnel.
The cyber-enabled workforce answers “yes” to two or more of the following questions:
- Do you use an Internet-connected computer to conduct a majority or a significant portion of your work duties?
- Do you have access to proprietary information such as customer data, contact lists, employee records, or other confidential business documents?
- If a bad actor had access to your computer or workstation along with access to the systems you use within your role, could it cause your organization significant financial damage?
- Do you interact with outside parties including partners or clients in some capacity related to cybersecurity products or services?
For cybersecurity to solve its workforce shortage, its future must be supported by talented team members across all departments who possess and demonstrate sound cybersecurity competencies. Organizations can generate momentum in cross-skilling cyber-enabled employees into more technical cybersecurity roles by first determining the baseline performance of those individuals, then utilizing their strengths to fill knowledge and skills gaps. In leveraging cyber-enabled talent from within their own organizations, they can ultimately take responsibility for narrowing the cybersecurity talent shortage.
Filling Cybersecurity Skills Gaps
The future of business as we know it will be supported by talented team members across all departments who possess and demonstrate sound cybersecurity skills in their daily activities. In order to support this reality, N2K has developed a data-driven training model designed for both cybersecurity and cyber-enabled personnel.
If you’re looking to build the knowledge, skills, and abilities of your team beyond cybersecurity awareness training, you can get in touch with us here or explore our specialized training solutions for the following groups:
Additional Resources
- [Webinar] Cyber-Enabled Workforce: What it Means & How to Ensure Your Company is Prepared. Watch on-demand >>
- [Case Study] Upskilling 400+ System Engineers to Drive Sales at Palo Alto Networks. Read the Case Study >>
- [Case Study] Boosting Cybersecurity Expertise for 1300 Clinical Engineers at TRIMEDX. Read the Case Study >>


