Welcome to the new year and the final installment of the Cybersecurity in the Pandemic series. At more than nine months in, business attire continues to sit collecting dust in the closet, and “You’re on mute” echoes daily on countless Zoom calls. As of October 2020, 70% of full-time workers in the U.S reported they are working from home during COVID-19 and most are content with staying in their home office for the foreseeable future. Unemployment is falling, now sitting at under 7% for the first time since April 2020 following its peak at 14.7% during that same month.
Since our first segment, also released in April, we’ve been monitoring hiring trends for cybersecurity talent by industry, geographic location, and workforce experience levels. While cyber talent has long been in-demand, COVID-19 has escalated the need for talent within certain industries. In Part IV, we observe demand within top industries such as healthcare, the great tech migration to Texas, and how leaders can advance their technology and people.
Taking [Cyber] Care in Healthcare
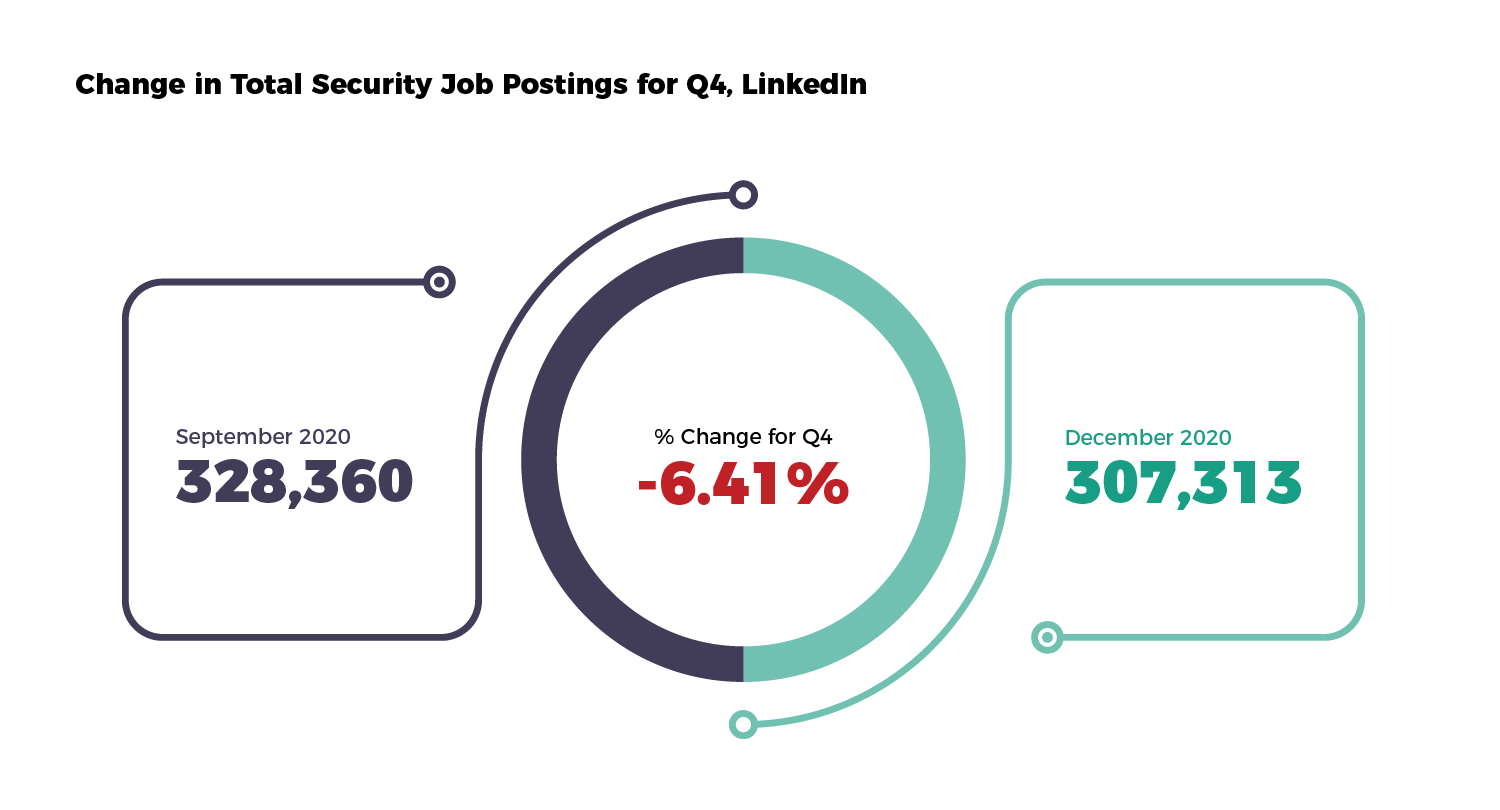
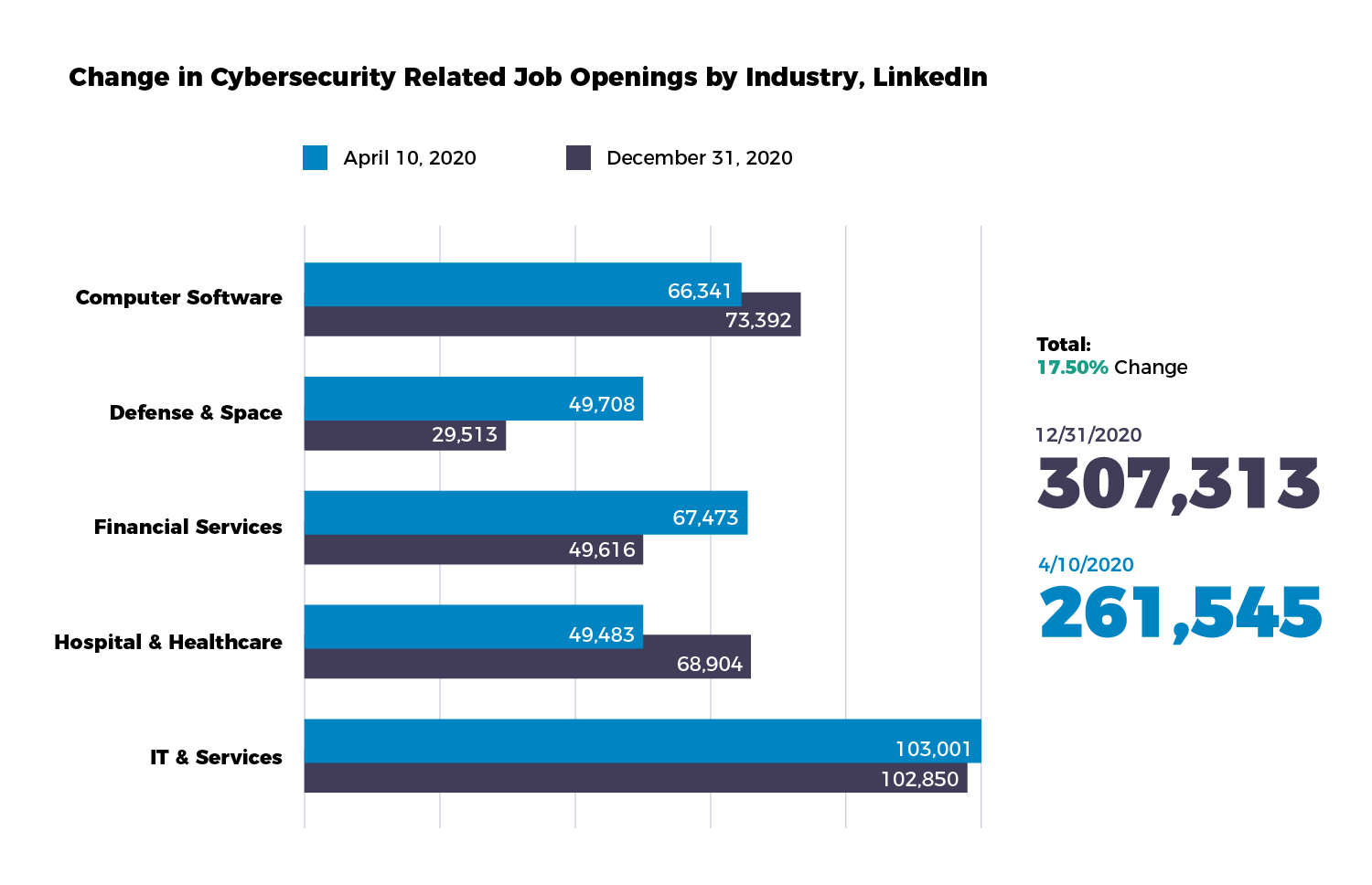
Overall job postings for cybersecurity roles have been on the decline in the fourth quarter with -6.41%, compared to the previous quarter. On average, however, demand has increased by 17.5% since April.
There are several factors that can attribute to the fluctuation in demand for security personnel. For example, the prioritization of onboarding new staff due to economic changes. While the stock market is by-and-large booming, it is important to separate that performance from the health of the overall economy. Many organizations are struggling financially, still coping with the significant fallout of the previous three quarters. While cybersecurity positions were not impacted immediately as other professional areas were, there is the possibility that it was simply delayed. Alternatively or perhaps additionally, organizations are finding opportunities to invest in technology solutions or external managed service providers to offset the need to hire internally. With the rise of cyber attacks on hospitals around the country, it’s no surprise of the concurrent rise in demand for security talent in the industry, up nearly 40% since the beginning of the pandemic.
Some healthcare organizations have taken proactive measures to ensure their staff possesses the security skills necessary to underscore their competitive advantage, elevate their employees and uphold the security posture of their company, service, and products.
Following a data breach in October, non-profit health system Centerstone is investing over $800,000 in IT security system upgrades as well as investment in workforce training. Leading clinical asset management company Trimedx partnered with N2K to provide specialized healthcare cybersecurity training for over 3,100 Clinical Engineers as part of their CE Cyber Academy.
On New Year’s Day, Congress objected to the President’s vetoes on the National Defense Authorization Act (NDAA) and effectively passed it into law. This bill includes several cybersecurity provisions that allow agencies like the Cybersecurity and Infrastructure Security Agency (CISA) to investigate hacks of private sector networks. This is a promising first step in prioritizing cybersecurity and taking action to preserve the security posture in the public sector. The demand for cyber talent no doubt will trend upwards throughout the year.
Big Tech in Texas
It’s not just individuals who are making moves across the country for a better cost of living as discussed in previous installments. Major tech companies are also relocating their HQ or expanding operations outside of Silicon Valley, and they’re heading for the Lone Star state.
 In a recent announcement from Oracle, they’re moving their headquarters to Austin, Texas after 44 years of residing in Redwood City, CA. Another tech veteran, Hewlett Packard Enterprise (HPE), is saddling up for Houston as well as electric vehicle titan, Tesla, has also set its sights on the ever-growing tech hub of Austin. The city may also now be familiar to some as “Silicon Hills”, observing Central Texas’ signature hill country. The great migration of big tech and the influx of young professionals over the years is not surprising – the state is most attractive for its lower tax rates, more affordable costs of living, and more “lenient” government regulations, among several other cultural and artistic qualities as well.
In a recent announcement from Oracle, they’re moving their headquarters to Austin, Texas after 44 years of residing in Redwood City, CA. Another tech veteran, Hewlett Packard Enterprise (HPE), is saddling up for Houston as well as electric vehicle titan, Tesla, has also set its sights on the ever-growing tech hub of Austin. The city may also now be familiar to some as “Silicon Hills”, observing Central Texas’ signature hill country. The great migration of big tech and the influx of young professionals over the years is not surprising – the state is most attractive for its lower tax rates, more affordable costs of living, and more “lenient” government regulations, among several other cultural and artistic qualities as well.
WFH FTW
Even with vaccinations currently in distribution, there’s still no telling when people can – or feel comfortable enough – to return to the office this year. Let’s be honest–all bets were off as to when any form of normalcy would resume after the announcement of the NBA bubble. Not long after Adam Silver’s announcement to delay the season, organizations around the country also had to move quickly to support as many employees as possible transitioning to a new working environment. For those fortunate to remain in a job or had found a new role that permits remote work, the majority wouldn’t be upset if they could skip the commute for good.
Chief Economist of LinkedIn, Karin Kimbrough, notes that among jobseekers, the volume of job searches filtering for “Remote” work on LinkedIn increased by approximately 60% since the beginning of the pandemic. Moreover, 1 in 2 people wouldn’t return to their job if they could no longer work from home after COVID-19. Of the same respondents, 80% indicated that they feel like their employers care about their well-being and work-life balance if remote work was permissible.
While there are more than 8,000 security roles that are either part time or full time remote, leaders have to weigh potential opportunities and risks to offer such benefits for current and future security personnel.
Advancing Tech AND People
The pandemic has propelled infosec leaders to either implement new or advance current technological initiatives faster than ever imagined. In doing so, companies can improve the customer experience, simplify operations, and innovate faster. And all these technologies require assessment and maintenance. Similar to implementing a vulnerability assessment on enterprise systems, the same considerations should be made for assessing the competency and capabilities of security personnel.
Organizations accustomed to bootcamps or unorganized online video libraries for security training are now forced to consider alternative solutions and in this search, leaders understand what exactly they’re missing from a thorough training program. Visibility, accountability, and concrete performance metrics, such as to ensure those who are ready to take a certification exam or prove proficiency in a role, are not provided in these solutions.
Make Training Meaningful
It is critical for organizations to understand and incorporate training that’s meaningful. Meaningful defined as being accurate, deliberate, and measuring the right things, in order to produce meaningful insights to both employees and leadership. For specific groups, whether based on function or seniority, keeping them engaged and implementing positive behavior changes can be difficult if the outputs from training are not relevant to the inputs or objectives required of said groups.
Large organizations like SAP are taking that challenge head-on, using both internal resources and external services to devise detailed road maps of proposed job families for the security department. Having a human capital management blueprint in place can help leadership better identify and define potential career pathways for their cybersecurity staff, as well as utilizing it as a navigation tool to improve onboarding and upskilling efforts.
Conclusion
If 2020 provided at least one good thing for individuals and organizations, it was the abrupt shake-up from the systematic monotony in operating and a “this is how we’ve always done it” mindset. It allowed us to truly ask ourselves “Is this actually helping us to achieve our business goals?” and “Is there a better way to do it?”
And if 2020 helped you to uncover the gaps in your current cybersecurity training program, N2K provides made to measure online solutions designed for direct cybersecurity personnel and cyber-enabled professionals.
Read the previous installments from the series:
Cybersecurity in the Pandemic Pt. I